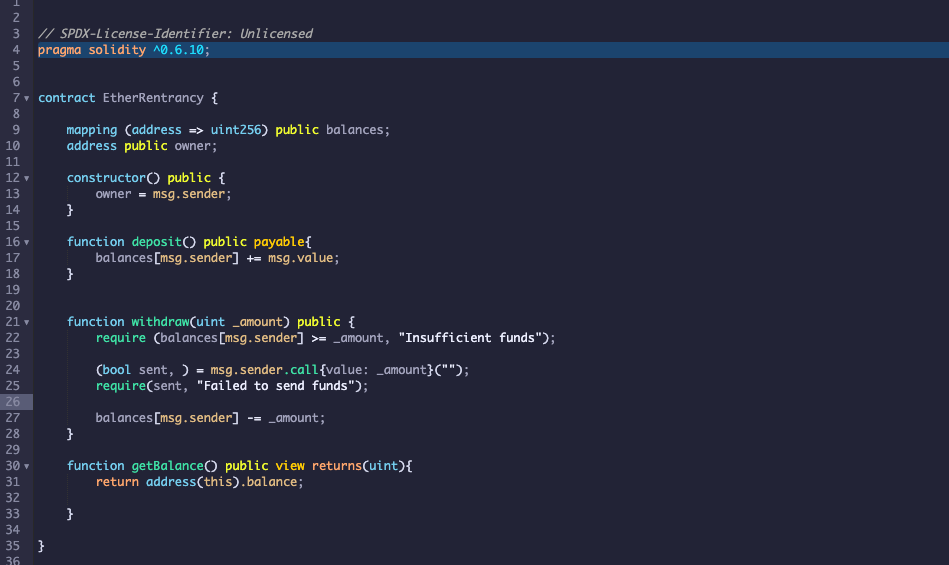
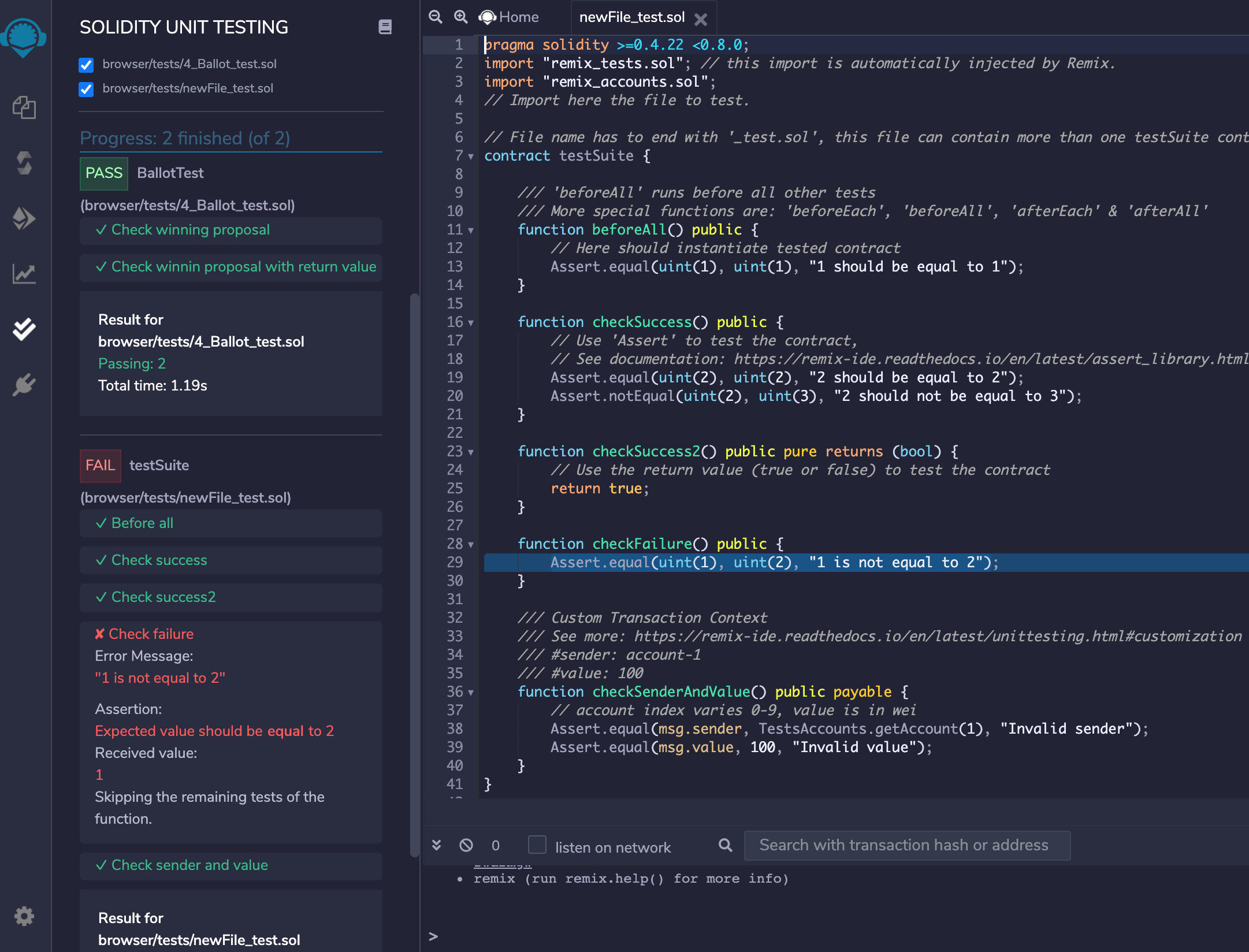
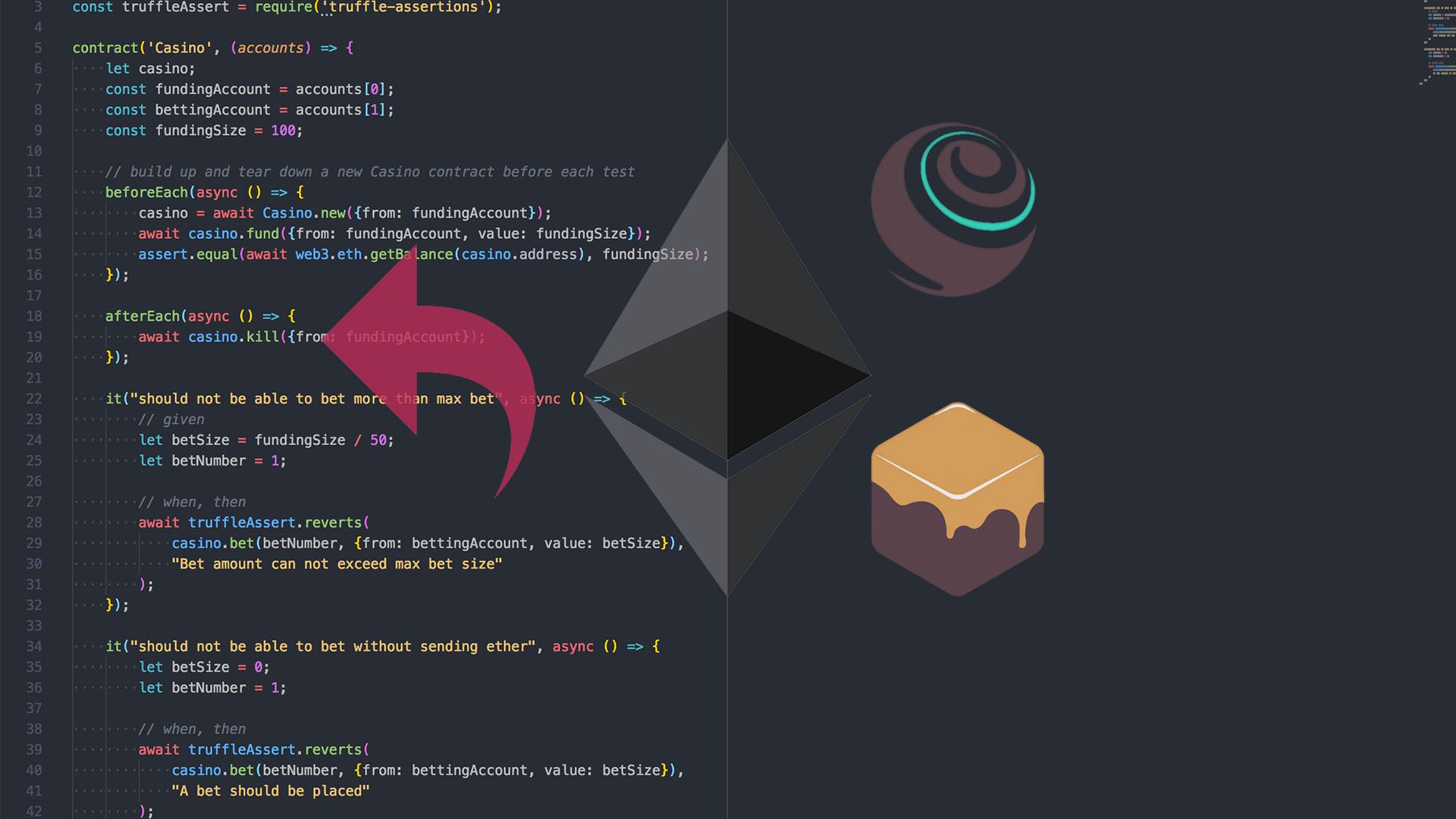
How to Secure Your Smart Contracts: 6 Solidity Vulnerabilities and how to avoid them (Part 1) | by Georgios Konstantopoulos | Loom Network | Medium
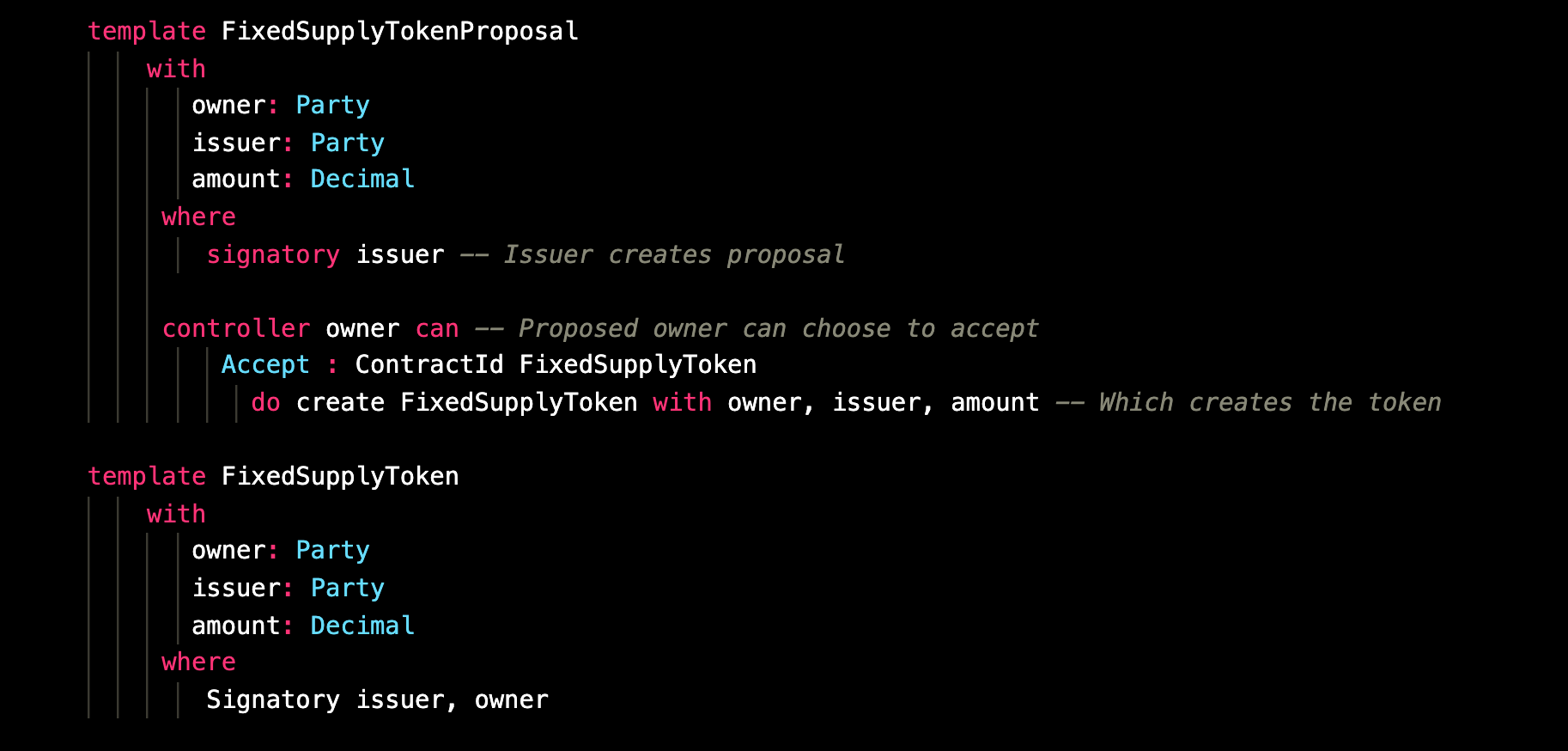
Entropy | Free Full-Text | An Analysis of Smart Contracts Security Threats Alongside Existing Solutions | HTML